Reduce your cyber risk with the Essential Eight, the security model recommended by the Australian government for SMBs.
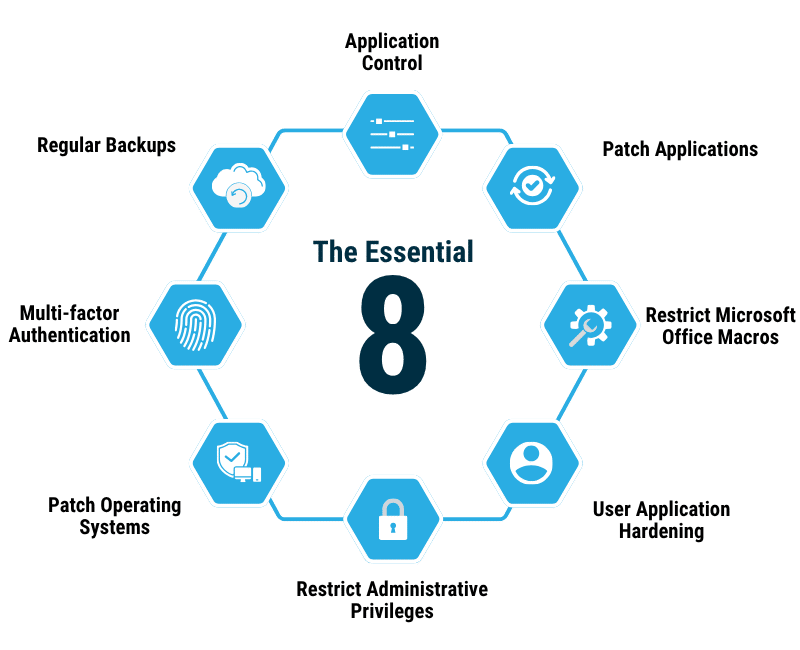
The Essential Eight is a set of cyber security strategies created by the Australian Signals Directorate.
Together, the 8 strategies provide a strong level of protection against modern attacks.
Because different organisations have different security needs, the Essential Eight has 4 maturity levels.
Small and medium businesses should meet Maturity Level 1 at minimum.
Each of the following strategies has multiple controls.

Keep your apps up to date.

Keep your operating system up to date.

Use MFA to access your apps and online services.

Only give admin access to people that need it.

Control the apps people can download.

Block unnecessary Microsoft macros

Block risky app activities.

Keep your backups confidential, intact, and accessible.

Implementing the Essential Eight starts with choosing a maturity level.
Level 1 is the minimum – most SMBs should aim for Level 2, and some high-risk organisations may need Level 3.
Once you’ve chosen your target, work with your managed services provider to start implementing the different controls.
You may already have some in place.
Others might require modernising old systems or improving your current processes.

The Essential Eight aren’t always easy to implement – especially if you have lots of users or a complex IT environment.
We can help explain exactly what a given control means and work with you to action it.
If business requirements make that too difficult, we can even help you explore alternate controls that still satisfy the Essential Eight assessment criteria.
All small and medium businesses should aim for a minimum of Maturity Level 1.

Your cyber security posture has weaknesses.

Your business is protected against basic cyber attacks.

You’ve reduced the risk of personalised, targeted attacks.

You’re capable of defeating more sophisticated adversaries.
If you’re already certified to standards like ISO 27001, you may have met or exceeded Maturity Level 2.
| Table Corner | Essential Eight | ISO 27001 | NIST CSF |
|---|---|---|---|
| Description | The Essential Eight is a set of 8 baseline mitigation strategies, each featuring multiple controls. | ISO 27001 is a standard for information security that includes policies, procedures, and controls. | The NIST Cybersecurity Framework (CSF) is a framework that includes 6 core functions. |
| Type | Maturity model | Standard | Framework |
| Protection Level | Baseline | Holistic | Holistic |
| Origin | Australia | International | US |
| Approach | Prescriptive | Prescriptive | Flexible |
| Located At | cyber.gov.au | iso.org | nist.gov |
Yes, all businesses, regardless of their size, should meet Essential Eight Maturity Level 1. That’s the baseline for any IT environment, even if you’re running a one-person company.
Keep in mind that most of the controls for ML1 aren’t particularly difficult to meet, especially for micro-businesses. Using Microsoft 365 and Windows 11, running basic security software like Defender, having MFA for your apps, and having daily automated backups will satisfy the majority of the controls.
Compliance does get harder as your business gains more staff – but that’s also when the risk and potential cost of an attack becomes higher.
It depends on the legacy system in question. The Essential Eight is designed for modern organisations, so some applications and operating systems – particularly unsupported ones – may be unable to meet specific Essential Eight controls.
In those scenarios, it’s sometimes possible to still comply with the Essential Eight by implementing an alternate control. Essential Eight assessments recognise that IT environments are complex and vary hugely across different organisations; even if a specific control can’t be used for some reason, you can still address the intention of that control through one or more alternatives.
If you can’t meet the Essential Eight controls and using compensating controls is too costly, though, that’s generally a good indication that your legacy system is a security risk. Talk to us or another cyber security provider about the best way to migrate to something more secure – keeping an active vulnerability in play is almost never a good idea.
No, the Essential Eight isn’t legally required for most organisations in Australia. Government departments normally have to meet ML2 or ML3, though, and some insurers may make Essential Eight compliance a condition for cyber insurance.