The third Essential Eight strategy, ‘Multi-factor authentication’, focuses on deploying hardened MFA across online services. Here’s what you, an SMB...
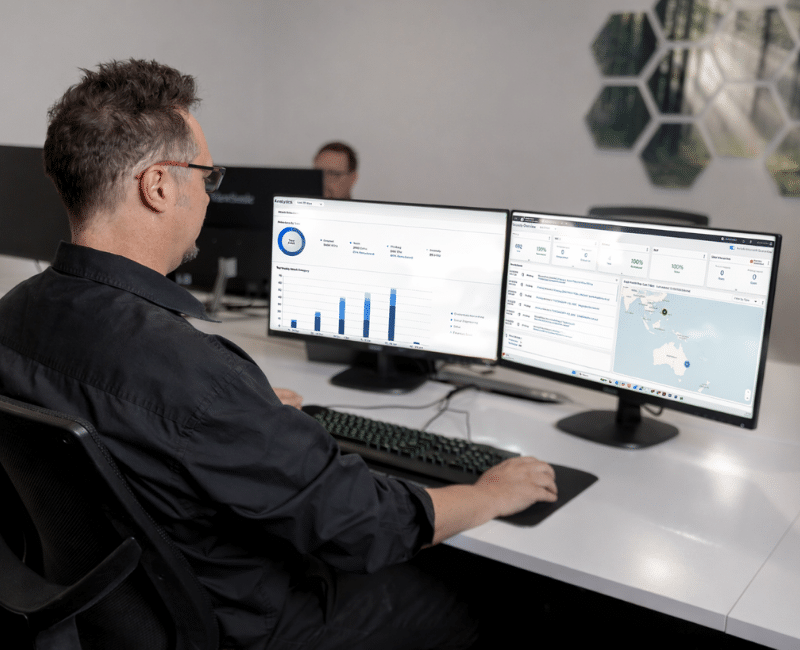
Protect your people’s inboxes from phishing attacks, malware, and other cyber attacks with AI-driven threat detection.

22+
years in business
200+
clients
15+
professionals

My staff inboxes aren’t currently protected.
We had a breach and I want to switch to better security.

My current email security is too aggressive.
Stop phishing attacks before they reach your inbox. Our AI-driven security system learns from past inbox interactions, making it less likely to register false positives.
Keep sensitive data away from people who aren’t authorised to view it. We’ll build in safeguards that prevent accidental email shares and encrypt confidential files for everyone except authorised users.
No email defence system is perfect. If a threat does slip past your inbox’s first line of defence, our software uses machine learning to identify and quarantine it – before your staff get exposed.
Backed by market-leading technology.
Business email compromise is the leading cyber threat for Australian businesses.
Thirty-four per cent of all attacks on businesses come through the inbox.

Your inbox isn’t your only vulnerability.
File-sharing services like SharePoint and Microsoft Teams are attack vectors too.
If one of your staff accounts is compromised, an adversary could use those channels to send malicious files that help them gain access to your network.
Our email security software can be deployed across all common file-sharing and chat programs – ideal for keeping all your comms clean and phishing-free.
Helping Queensland brands conduct cybersecurity audits
since 2003.
DomainKeys Identified Mail (DKIM) is a type of email authentication. It lets email servers check whether an email that says it came from your domain actually came from your domain. DKIM has 2 parts:
When a server receives an email from your domain, it checks the DKIM header in your email against the DKIM record. If the DKIM header is verified, the server will consider the email authentic and let it through.
For example, an adversary might try to send a phishing email from ‘hi@itleaders.com.au’. They could set their ‘From:’ field to hi@itleaders.com.au and simply send out the email. If our domain didn’t have a DKIM record, email servers couldn’t confirm whether the email actually came from us or not – the adversary would successfully impersonate us.
Domain-based Message Authentication Reporting and Conformance (DMARC) is a protocol for handling emails that fail to pass DKIM and other checks. Your IT team can set your DMARC policy to mark failed emails as spam, for example, or quarantine them in a separate folder.
Yes, you should have multi-factor authentication (MFA) for all email logins. It’s required to meet all cyber security standards. Without MFA, any kind of password compromise means that an adversary can easily access your email and, from there, infiltrate your network.
‘Spoofing’ occurs when an adversary impersonates someone else over email. For example, someone could pretend to be a supplier you work with, a colleague, or even software support. In a spoofing attack, the impersonated account isn’t actually compromised – the email just appears to be from that person (normally by using a very similar email address or fake sender name).
One of the more recent spoofing methods targeting Microsoft 365 users is the Direct Send exploit. Adversaries use 365’s Direct Send feature, which lets internal emails pass between 365 apps without verification, to mimic emails from real people in your organisation. In many cases, the spoofed emails actually seem to come from the recipient themselves (normally, with a malicious file or link attached that the recipient then clicks out of curiosity).
Like many successful cyber attacks, spoofing is relatively simple – and that’s exactly why it works. The best way to keep your people safe is to invest in good email security and ongoing cyber awareness training.
You can’t stop email phishing and other types of BEC attacks. If you run a business, you’ll almost certainly be targeted by scammers – in some cases, multiple times each day. You can, though, implement countermeasures that keep you and your people safe.
Here’s a brief overview of defences you should have in place.
If you receive an email with one of the following signs, it could be a phishing email.
You can read more about the different phishing styles (and how to prevent them) in ‘Six Signs of Business Email Compromise to Watch For’.
Learn how better cyber security can protect your organisation from modern threats – including business email compromise.